Source Link Privacy.

Tarlogic Security has detected a backdoor in the ESP32, a microcontroller that enables WiFi and Bluetooth connection and is present in millions of mass-market IoT devices. Exploitation of this backdoor would allow hostile actors to conduct impersonation attacks and permanently infect sensitive devices such as mobile phones, computers, smart locks or medical equipment by bypassing code audit controls.
We really should be pushing for fully open source stack (firmware, os) in all iot devices. They are not very complicated so this should be entirely possible. Probably will need a EU law though.
Backdoored devices are useful for people who can impede that.
And the way EU is approaching privacy, surveillance and all such, - oh-hoh-ho, I don’t think there will be a EU law.
I 100% believe firmware should be open source no question about it. There’s so many devices out there especially phones and iot devices that just become e-waste because you can’t do anything with it once it’s not supported if it was open source and documented in some way then it could be used. I have like five cheap phones that I got because they were so cheap but once they lost support they’ve become completely useless even though they still work.
Yeah tons of weird little private softwares never get updates, but they aren’t making anyone money either
Well… Shit.
There are so, so, so, many ESP32’s in not just my house, but practically everyone I know.
There outta be fines for this BS.
You’re fine. This isn’t something that can be exploited over wifi. You literally need physical access to the device to exploit it as it’s commands over USB that allow flashing the chip.
This is a security firm making everything sound scary because they want you to buy their testing device.
You literally need physical access to the device to exploit it
You don’t need physical access. Read the article. The researcher used physical USB to discover that the Bluetooth firmware has backdoors. It doesn’t require physical access to exploit.
It’s Bluetooth that’s vulnerable.
I just re-read the article and yes, you still need physical access.
The exploit is one that bypasses OS protections to writing to the firmware. In otherwords, you need to get the device to run a malicious piece of code or exploit a vulnerability in already running code that also interacts with the bluetooth stack.
The exploit, explicitly, is not one that can be carried out with a drive-by Bluetooth connection. You also need faulty software running on the device.
“Depending on how Bluetooth stacks handle HCI commands on the device, remote exploitation of the backdoor might be possible via malicious firmware or rogue Bluetooth connections.”
I of course don’t know details but I’m basing my post on that sentence. “Backdoor may be possible via … rogue Bluetooth connections.”
Looking at the article, the exploit requires you to be able to send arbitrary data to the Bluetooth device over a physical connection. This means that a properly secure application will be protected from drive by connections, but if the application has an exploit that either lets an attacker write arbitrary values to the Bluetooth controller, or more likely contains a general arbitrary code execution exploit, then you could use this to rewrite values to the chip that would let you “persist” certain changes to the Bluetooth chip that would be difficult to notice.
I would consider this a moderate concern, as this will definitely increase your options if you’re looking to be able to make an attack that targets a specific device and this gives you a few additional persistence options, but any attack would have to be designed for a particular program running connected to a Bluetooth chip.
A more likely concern in my opinion would be the possibility of a supply chain attack, where someone compromises a Bluetooth chip that they know will be used to construct a particular part.
I don’t think that it’s super likely that either of these will affect the average person, only corporations and governments where espionage is an actual threat, as if you can find a Bluetooth IOT device that you want to mess with, like a Bluetooth enabled door lock, then you’re more likely to be able to find an arbitrary code execution attack which causes it to unlock immediately. Being able to spoof a different Bluetooth device isn’t likely to give you that big of an advantage when you’re working with a device that was already vulnerable for a different reason.
thank you for the nice analysis. this should really be voted highest.
Thank you for the analysis, very insightful!
Do you reckon this is more of an oversight or bug in the BT stack, or a deliberately places backdoor as the title seems to suggest?
Depending on how Bluetooth stacks handle HCI commands on the device, remote exploitation of the backdoor might be possible via malicious firmware or rogue Bluetooth connections.
I really wish these articles just tell us what these scenarios are. I understand companies need publicity or need to sell software but if it isn’t replicatable and the article says “might be possible” it kind of sounds like a secuity sales pitch.
This is especially the case if an attacker already has root access, planted malware, or pushed a malicious update on the device that opens up low-level access.
This part basically sounds more like a software issue where the attacker has a way in already. The system is already vulernable at this point before using the exploit found.
I don’t think there’s enough information out yet.
It is very interesting though.
I do have a few outside. Probably not the best security-wise. Haha. Those are the first to get patched when one comes out.
Security wise, unless you are being specifically targeted by someone, you are almost certainly fine. And if you are being specifically targeted, I think someone hacking your ESPs is the least of your worries. A malicious attacker that knows your physical location can do a lot more scary things than just spying through ESPs.
Just wait until a jester creates a software that sends an erase flash backdoor command to any BT device it sees.
In that case, how long til some open source project uses it to make a custom firmware to bypass the manufacturer bs and integrate my cheap IoTs seamlessly into Home assistant?
You can already reflash a lot of devices for this purpose. And you could use esp-home to customise once reflashed
Really? Where can I find this
Heres the top google link i found: https://randomnerdtutorials.com/how-to-flash-a-custom-firmware-to-sonoff/
Esp-home is available as a HA addin, docs here: https://esphome.io/
Thanks
Esp-home also works with the older esp-01 - it was released as a wifi module so there are only two gpio’s, but thats enough for a lot of home automation stuff.
Here’s one i have connected to HA, where HA uses rest-api to capture some data from a game called tacticus, and it shows my available tokens for guild raid and arena

Tasmota is another option if they have your specific device in their list. Otherwise you have to do some debugging to figure out what gpio or i2c address to use.
I think we are basically already there with ESPs :D.
Wrong. Read the analysis. It is a BT vulnerability. One can probably design a cheap attack system that just sends a erase flash command to any BT device in reach, instantly bricking every BT enabled ESP32 device.
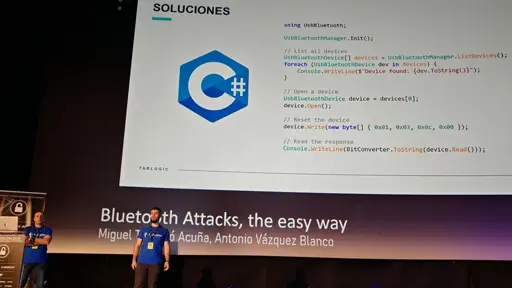
Just reread it and no, it’s not a BT vulnerability. The “erase flash” command is something that has to be done by software running outside the BT stack. You can even see that inside the slides. The
UsbBluetoothsoftware is connected to the device with the flawed bluetooth chipset.The vulnerability is that if you have this chipset and compromised software, someone can flash the chipset with compromised flash. They even say that it’s not an easy attack to pull off in the article.
In general, though, physical access to the device’s USB or UART interface would be far riskier and a more realistic attack scenario.
In otherwords, the attack is something that can only be pulled off if there’s also a security vulnerability within other parts of the hardware stack.
Yeah, that’s not the main concern.
I hate it when an attacker who already has root access to my device gets sightly more access to the firmware. Definitely spin up a website and a logo, maybe a post in Bloomberg.
This sounds like there are some undocumented opcodes on the HCI side – the Host Computer Interface – not the wireless side. By itself, it’s not that big a deal. If someone can prove that there’s some sort of custom BLE packet that gives access to those HCI opcodes wirelessly, I’d be REALLY concerned.
But if it’s just on the host side, you can only get to it if you’ve cracked the box and have access to the wiring. If someone has that kind of access, they’re likely to be able to flash their own firmware and take over the whole device anyway.
Not sure this disclosure increases the risk any. I wouldn’t start panicking.
Too much fanfare and too little real info shared to be of any value. Sounds more like an ad than infosec
Seriously wtf did I just try to read? It sounded like AI slop.
The other day someone posted in Canada community that Canada should stop using Tesla cars and import Chinese cars. I replied saying, “That’s like replacing one evil with another.” I was downvoted by a lot of people. I should’ve expected it cuz a lot of people have short term memory.
Because that’s not about privacy, that’s about the trade war. Retaliatory tariffs on US cars increase cost of cars for Canadians, as there are almost no car assembled in Canada. Reducing or eliminating tariffs on cars from China would lower cost of new cars for Canadians while keeping the tariffs up.
For privacy and security, not a single new car on the market is decent right now. That should be regulated, but that’s no concern for any politician at the moment.
Europe and its 50 car makers could also be considered instead of China…
CCP has backdoor into every tech that comes out of China. It’s not about just privacy. They control democracies based on shaping narratives. They’ll utilize everything that democracy offers and use it against countries. They don’t have freedom of speech or press so they themselves are not victims of it. EVs are really just computers on the road. Flooding the market with Chinese EVs would just mean creating a massive free network on a foreign soil for them.
There’s been a lot of that lately. Same here in New Zealand.
You dipshits, they’re both the bad guys now.
A lot of people are dumb. Or maybe because they feel offended because they are Chinese, but the reality is that every Chinese company is ultimately controlled by the CCP. If I was fighting a cold war, I would do the same. Sell compromised devices to my trade partners (AKA enemies) so I have leverage when I need it.
the reality is that every Chinese company is ultimately controlled by the CCP.
Yes.
But in the same way that every US company is ultimately controlled by the US Government. And every EU company by them. And every other country by their own government.
People act like traditional car manufacturers don’t exist anymore even though they all over EV options…
Everyone has short-term memory and long-term memory. You’re misunderstanding precisely what “short-term memory” refers to. Short-term memory is held for a short time before it’s converted to long-term memory. What you’re referring to is being short-sighted. As in people who don’t fully think about the long-term consequences of current actions. Said short-sighted people still have both short and long-term memory. They’re probably just a little dumb so they don’t fully utilize the memories stored long-term.
“China bad” because western media says so. Please disregard the billions of dollars spent by western governments to ensure you keep thinking that way.
It’s just another capitalistic country no better or worse than Canada or the USA. Though, the Chinese government has said their intention is to move towards socialism, so good for them. I’m stuck over here witnessing fascist billionaires loot the government/working class.
Thats super interesting! Write a poem about three gorges dam please
Well, no, China is bad because freedom is very restricted there and because they have ambitions to dominate the world.
Yes, every other world power in the world is more or less the same. People cannot, in general, be trusted to be “good” when given the opportunity to abuse. A world power can be held in check by the presence and efforts of other world powers, though.
I’d like to know if this is just a firmware update or unfixable, but sadly this seems just an ad rather than news
Here’s an article with a bit more detail… but I’m still unclear whether these backdoor commands are hardware circuits or firmware logic.
Bleeping Computer: Undocumented “backdoor” found in Bluetooth chip used by a billion devices
Solid article. I imagine the folks at the cyberwire podcast will be doing more digging over the weekend for a solid summary come Monday.
Thanks for the link, this article is more clear compared to the posted above.
I’m more interested to the scope of the exploit whether it could touch the flash of the controller or not as you can also do OTA update through the BLE component.
deleted by creator
Even if it were fixable, it would be up to manufacturers to push updates. I doubt any really care enough.
It is not easy to determine how fixable this is. IIRC, the ESP32 has the wireless stack hidden from user space, and I am not sure if it is a blob included during link time, or if it is stored in a ROM of the chip. I do have the chips and the development enviroment in my studio, but (luckily) I decided to use a different chip for my project.
But I know there is a load of systems using either the ESP32 as their main processor, or as an auxiliary processor to add WiFi or BT capabilities, so this really is a big oh shit moment.
The Chinese adding back doors into their software/hardware.
Say it ain’t so!
Say it ain’t so
Your bug is a heartbleeder
Say it ain’t so
My NIC is a bytetakertech backdoors are only okay when us good guys require em
China ain’t our friend but neither is our own regime, I don’t get the normies only caring about privacy and security when chinaman do the thing
Then they tuck their dicks because they got nothing to hide when domestic spook is doing the same
pathetic and intellectually disingenuous
Where did anyone say anything remotely like that?
I think it’s sarcasm mate.
How about all tech backdoors are bad and we should aim to use and make software and hardware that is ethically produced and usable without selling out your privacy and security?
Like a PRISM for China, is every powerful country just backdooring each other?
Thats hot.
It ain’t so.
To use the “backdoor” an attacker needs to have full access to the esp32 powered device already.
It’s like claiming that being able to leave your desk without locking your PC is a backdoor in your OS.
I couldn’t find a list of devices. Anyone else find one?
The article is talking about the Espressif ESP32 micro controller (has Wi-Fi/Classic Bluetooth/BLE).
I don’t know if the variants of this chip also have the same vulnerability (my guess is yes). As someone who works on this chip, I’m interested in more discourse on this matter.
Yeah, I caught the ESP32 part and tried to search for what devices these chips were built into, but couldn’t find one. I was curious how widespread the flaw was - as in, what consumer or infrastructure devices they might be in.
The Tasmota firmware documentation has a decent list, but it’s limited to devices that are known to be flash-able so you can install custom firmware on them. https://templates.blakadder.com/
Thanks, that’s a pretty short list - as you said it’s limited.
If it affects all ESP32s, the list is infinitely longer
Oh those kind of devices. Its very popular for hobbyists and self-designed devices or cheap IoT products. Don’t know the market presence outside Asia but its quite popular in India due to its low cost.
I’d also like to hear more. I have at least a dozen of these in my house.
One more reason to have actual open-source drivers instead of binary blobs…
Not the first time a backdoor was found on Chinese made hardware and it won‘t be the last time. Decoupling can‘t happen quickly enough.
Which government’s backdoors would you prefer?
“We know you have a choice in oppressive governments, so we appreciate you choosing ours.”
None of them, that’s why the only things in my house that connect to the internet are my computers, game consoles, and cell phone
Assuming you’re not joking here, if your computers are any way modern they almost certainly have a backdoor.
Obviously, but I trust my Linux mint laptop a hell of a lot better than my aunt’s XIPPLG branded wifi cat feeder that she bought off Amazon
I don’t think Lemmy shitposters are getting them premium zero days used on them.
This isn’t some crazy zero day, it’s pretty well known. Intel management engine and AMD secure technology.
I guarantee all off those have components from manufacturers that a government could pressure for a backdoor.
You are correct, and it doesn’t change my stance at all. It’s still worth it to mitigate risk even if you can’t mitigate all risk.
Like, the fact that my 3d printer is already a fire hazard does not justify leaving a bunch of candles unattended
Not sure if joking or naive…
Like I said 6 hours ago, just because I can’t mitigate all of the risk doesn’t mean that I shouldn’t mitigate as much as I reasonably can.
My 3d printer is a fire hazard, but that’s no excuse for leaving a bunch of candles unattended.
Ah I missed the other comment, my client still had a cached view apparently. And definitely true regarding mitigation, your phrasing just read funny to me :)
True, but the ESP32 is used by a lot of devices. This backdoor is pretty huge in scope of devices impacted.
It depends on what the method of attack is. I’m not seeing anything saying that it would be possible to exploit wirelessly, so this could easily be mostly a non-issue.
I mean, most users here are browsing using a device with an AMD or Intel CPU, both with known backdoors. Not the first time a backdoor was found on American made hardware and it won’t be the last.
Jokes on them, I live in America when all that shit was already being done.
Is this some hardware flaw, or just something in their standard BT stack?
I was wondering the same thing. Wasn’t clear on whether these backdoors are there on purpose or because of mistakes
Removed by mod
I read in another article that the identified 28 backdoor commands.
I have a bunch of ESP32’s that … I can update and replace the firmware on, if i reset it the right way with a usb cable. the web site doesn’t explain it any way how this is any worse than that…?
The website is also the guy trying to sell the solution so I’m just sceptical for now
This can be done wirelessly, if the custom driver has been installed.